Ivanti’s Patch Tuesday breakdown goes beyond patching your applications and brings you the intelligence and guidance needed to prioritize where to focus your attention first. Catch early analysis on our Ivanti blog, then join industry expert Chris Goettl for the Patch Tuesday Webinar Event. There we’ll do a deep dive into each of the bulletins and give guidance on the risks associated with the newly-identified vulnerabilities.






![Copyright © 2026 Ivanti. All rights reserved. 28
February Known Issues for Windows 11
▪ KB 5075942 – Windows Server 2025 Datacenter Azure Edition - Hotpatch
▪ [WSUS] Per Microsoft Windows Server Update Services (WSUS) does not display
synchronization error details within its error reporting. This functionality is temporarily
removed to address the Remote Code Execution Vulnerability, CVE-2025-59287
▪ KB 5075899 – Windows Server 2025
▪ [WSUS]](https://image.slidesharecdn.com/february2026patchtuesday-260211220435-41a907da/85/February-2026-Patch-Tuesday-hosted-by-Chris-Goettl-and-Todd-Schell-28-320.jpg)
![Copyright © 2026 Ivanti. All rights reserved. 30
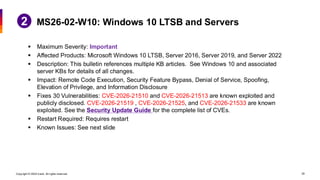
February Known Issues for Windows 10 LTSB and Servers
▪ KB 5075906 – Windows Server 2022
▪ [WSUS] Per Microsoft Windows Server Update Services (WSUS) does not display
synchronization error details within its error reporting. This functionality is temporarily
removed to address the Remote Code Execution Vulnerability, CVE-2025-59287.
▪ KB 5075897 – Windows Server 2022, 23H2 version
▪ [WSUS]](https://image.slidesharecdn.com/february2026patchtuesday-260211220435-41a907da/85/February-2026-Patch-Tuesday-hosted-by-Chris-Goettl-and-Todd-Schell-30-320.jpg)